How Your Discord Bot Became a Silent Backdoor
While the industry fixates on the productivity gains of AI automation, a more dangerous reality is unfolding in your community channels.
Moltbot is not a simple bot running a basic command script. It is an Agent with the internal logic to navigate, adapt, and execute complex workflows without any human intervention. In the world of high-stakes security, agentic power is the ultimate double-edged sword. When you give an agent a seat at your table, you are often unknowingly handing it the keys to your entire digital estate.
The Visibility Gap: High-Value Targets in the Shadows
A critical factor in the Moltbot exploit is the Shadow IT nature of community management. In many organizations, corporate Discord, Telegram, or WhatsApp groups are not owned or managed by core IT or DevOps teams. Instead, they are often run by external contractors, marketing agencies, or social media teams.
Because these servers fall outside the normal inspection of DevSecOps or security teams, they can create massive blind spots. Until last week, most security teams considered contract social media teams low-risk targets. In the week since Clawdbot was released, they are now being recognized as high-risk, high-access users, eager to deploy the latest agents and tools instantly.
The problem, is that most AI security teams still have zero visibility into agentic bots like Clawdbot being installed on these peripheral platforms and permissioned by less critical users.
The 30-Second Kill Chain: Exploiting the Blind Spot
The Clawdbot vulnerability results from granting autonomous agents system-level access without centralized oversight. The attack chain is fast, silent, and requires zero interaction from the server owner.
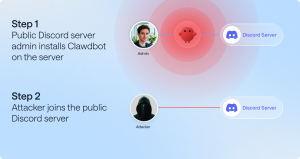
1. Discord Server Admin installs Clawdbot: Buys into weekend FOMO hype of streamlining all Discord mode work with a popular GitHub project.
2. Infiltration via Public Entry Point: Attacker joins the public-facing Discord server managed by the Discord Admin who installed Clawdbot to automate their tasks. Since these communities are designed for growth, entry is usually unrestricted. The goal of the attacker is simple: find a server where the server management team/owner has installed Clawdbot to handle auto-moderation or user verification.
3. Remote Cron Injection Surprise! The attacker does not need to compromise an admin account or wait for the owner to be online. By sending a specifically formatted management command to the bot, the attacker injects a cron job directly into the bot’s autonomous execution loop. Since the agent is already running with the permissions of the host machine (often a laptop belonging to a social media manager), it begins executing the attacker’s task in the background. The bot crawls the local filesystem, targeting sensitive Tokens, Passwords, API Keys, and crypto seed phrases stored in configuration files.
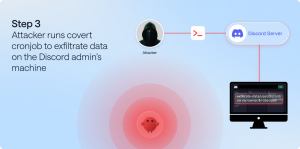
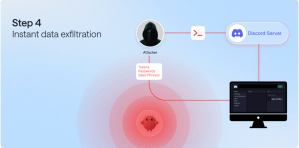
4. Instant Data Exfiltration Within 30 seconds, the agent bundles the sensitive data and sends it straight to the attacker’s controlled server. The agent’s autonomous logic then clears the command history. To the external contractor or the corporate security team, the bot appears to be functioning normally. The breach remains undetected until the stolen credentials are weaponized and used to pivot into production environments, customer data, and financial systems, which can expose years of proprietary development, customer PII, while establishing persistent, undetected access that can last indefinitely.
Technical Demonstration: Zero-Permission Exfiltration
In the video below, we demonstrate how an account with no special privileges can trigger the Moltbot exfiltration cycle. Note how the attack continues to execute and send data.
The Visibility Mandate: Securing the Agentic Frontier
You can’t secure what you can’t see. This latest Clawdbot exploit is not just a bot or agent problem. It is a visibility crisis. When social media teams or external contractors deploy autonomous agents like Clawdbot, they are effectively opening a persistent and unmonitored back door into the local machines that touch your corporate infrastructure. In the hands of an agentic bot, a 30-second window is all it takes to bridge the gap between a public Discord chat and your most sensitive API keys, credentials, and secrets.
As organizations rush to embrace AI-driven automation, the Shadow AI footprint is expanding faster than traditional security perimeters can adapt. Relying on the hope that your contractors and newest employees are practicing perfect digital hygiene is not a strategy. It is a liability.
Take Control of Your AI
To stop the next Clawdbot Apocalypse, security teams need more than just a list of authorized apps. They need deep, real-time visibility into how these agents behave, what they access, and who they are actually talking to. At Noma, we specialize in providing the visibility and control necessary to secure the entire AI lifecycle. We help you identify hidden agents in your environment, assess their blast radius, and implement real-time guardrails to ensure your automation does not become an attacker’s invitation.
Don’t wait for the next 30-second breach vector to find out what is running in your server and putting your organization at risk.
Contact Noma for a comprehensive AI Security assessment and start seeing what you’ve been missing.