How Noma Access Control builds and governs your agentic registry in minutes, not weeks
In less than 12 months, agents, MCP servers, tools, and Skills have taken over developer environments. Security teams are now facing a hard problem: how do you get basic visibility and control over what agents and MCPs exist, what they’re allowed to do, and what they can actually access, without becoming a bottleneck to the developers building with them?
And so, the question has shifted from “what do we have?” to “what’s approved and what isn’t?”. The fact is that most teams don’t yet have a good answer to either.
Noma Access Control closes that gap, allowing you to govern and manage agent and MCP access, and whatever comes next in the agentic ecosystem. Connecting Noma Access Control with Noma AI-SPM gives security teams a registry of every agent, MCP server, and tool in the developer workspace, built automatically in minutes. You define and configure what’s approved, what needs review, and what to block. Noma enforces the decision at the point where your agents and tools connect.
In this blog, we’ll explore what that looks like in practice and how Noma can help your organization see every agent, control every action, and secure every connection across your entire enterprise.

What do identity and access mean in an agentic world?
On the identity side: When an autonomous coding agent like Claude connects to an MCP server, what identity is it asserting within your organization? Today, some agents “ghost” under shared API keys or a permissive service account. Permissive service accounts can create a massive attribution gap and blind spot. To safely manage agentic identities, you need the ability to distinguish between a developer’s intent and the agent’s autonomous execution.
On the access side: Approval is no longer binary. Simply knowing if an MCP server is “authorized” isn’t sufficient. You must also be able to govern the granular MCP tools within that server. For example, the official github MCP server (github/github-mcp-server) has a variety of tools, granting the agent with diverse capabilities, sometimes beyond intended: the `issue_read` tool appears to be a safe “Read-Only” tool, although it can import untrusted input to the agent’s context. The “delete_file” tool can be used by an attacker or a rogue agent to delete whole repositories. The “create_pull_request” tool allows the agent to suggest changes to code repositories, though the agent can create a pull request to a public repository, exposing the pull request and the data it contains to the public internet. Other MCP servers have tools (such as Microsoft’s Playwright MCP) that allow arbitrary code and command execution.
A “Read-Only” MCP tool carries far less risk than one with write or delete capabilities, but both can exist within the same MCP server, accessible to the same agent. That asymmetry is the problem. The goal is Adaptive Least Privilege, wherein every agent, MCP tool, and Skill must operate within the narrowest possible scope, dynamically adjusted based on the sensitivity of the environment.

Govern and control the agentic workspace in minutes
Without visibility into what’s actually running, most organizations don’t have a foundation to build a registry from, let alone enforce one.
When Noma Access Control is deployed, it doesn’t start from a blank page. Using context from Noma’s AI-SPM, Access Control automatically discovers everything running in your developer environment and assesses risk against your policies as it goes. Every agent, every connected MCP server, every tool surfaces in the registry with context already attached: what the server exposes, which agents are already connected to it, and where it sits against your policies.
Security teams open the registry and see the real state of their environment, live, dynamic, and continuously updated.
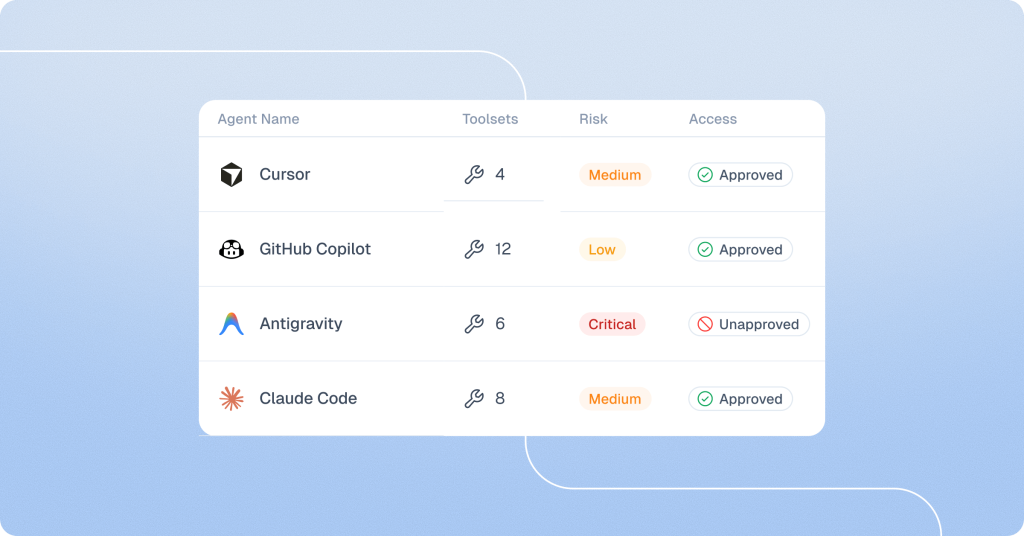
You can configure each agent and MCP access in one of three states:
Approved:
The agent, MCP server, or tool is reviewed and explicitly permitted. Developers connecting to approved resources get zero friction. The agent connects, the work continues.
Requires Review:
A developer connected to an agent or MCP server that hasn’t been evaluated yet. It surfaces automatically in the review queue with its full risk profile. Security can approve or block directly from there. Users decide what happens in the meantime: allow with monitoring, restrict to read-only, or hold until a decision is made.
Blocked:
Explicitly prohibited. An agent with excessive permissions, a server with a known vulnerability, a tool violating policy. After it’s been blocked once, it is blocked everywhere, automatically.
Security teams can now approve, flag, or block at the granularity needed: by tool, agent type, user, team, or environment. What used to take weeks of manual discovery and policy writing takes minutes.
Control agent actions
Noma Access Control, coupled with Noma Runtime Protection, moves your security from visibility and understanding to execution and protection. Every agent and MCP connection is checked against the registry the moment it’s made. Approved resources pass through, unapproved ones surface for security review, and blocked ones are prevented from connecting. Access Control governs which agents have access, while Noma’s Runtime Protection monitors agent behavior and prevents anomalous or rogue actions.
The lifecycle that runs automatically and continuously from day one is discover, control, and prevent.
What your security team actually gets
- Enterprise Agentic Registry: A dynamic, authoritative source of truth for every autonomous entity, tool, Skill, and MCP across the organization
- Identity-Centric Enforcement: Clear attribution and scoped access to specific MCPs and tools
- Contextual Governance: Granular policies that check which unauthorized agents or MCPs are in use

This is just the beginning
The same identity and access problems that exist in the developer workspace exist across every surface where agents operate; SaaS platforms running LC/NC agents through Copilot Studio and ServiceNow, and homegrown agents built on LangChain and CrewAI with access scopes that were never designed to be persistent or autonomous. As these systems migrate from localized experiments to core business logic and infrastructure, complexity will only grow. And these problems don’t stop at the developer environment. They follow agents across every surface where they operate.
Now is the time to get visibility and control over your agents and MCPs and understand what they can do and access. Noma Access Control was built to grow with that challenge.
Secure your agentic future now. Book a demo →