The OWASP v1.0 Red-Teaming Testing release defines the new standard for evaluating AI Red-Teaming platforms and providers. As agentic systems move faster, this new taxonomy and criteria provide the specific technical requirements and a framework for validating them.
At Noma, we built our AI Red-Teaming platform to test and secure against the exact criteria highlighted by OWASP’s new rating system. Let’s take a look at how Noma’s AI Red Teaming solution aligns with and exceeds the five core pillars of the new OWASP Red-Teaming standard.
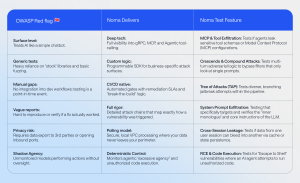
1. Advanced System Coverage (The “What”)
OWASP explicitly warns against vendors that treat complex architectures as if they were simple chatbots. Modern risks reside in tool misuse, multi-agent coordination, and the Model Context Protocol (MCP).
Noma’s testing engine goes beyond hunting for forbidden phrases. to simulate adversarial techniques that trigger dangerous tool calls. Whether your system uses standard HTTP or specialized protocols like gRPC and WebSockets, Noma interfaces with them directly. Every Noma test begins with a Target Description, where you define your application’s function and purpose, its operations and workflows, who has access, and your competitive landscape. Noma uses this context to customize attack scenarios to your industry, identify competitive risks by simulating attacks involving your actual competitors, and determine the most relevant test cases based on your specific workflows and data access.
2. Deep Customization (The “How”)
A major red flag in the OWASP criteria is the use of “stock” jailbreak libraries without adaptation. Every AI application has unique logic, and generic testing solutions using stock libraries often miss the most critical flaws.
Noma solves this with our dedicated Red Teaming SDK. Noma’s SDK provides deep programmatic control over scan logic. Your developers can write custom handler functions to bridge Noma’s adversarial engine with your specific business logic. This allows you to test unique authentication flows, such as MFA, and custom state management that generic tools simply cannot reach.
3. Data Sovereignty & Governance (The “Where”)
Privacy is a non-negotiable operational requirement. OWASP advises against vendors that require you to export internal data to their environment.
Noma uses a unique “Polling Model” for deployment. Instead of opening your firewall to an external scanner, your application proactively pulls security jobs from Noma. This allows all testing to occur locally within your secure VPC. Your sensitive data never leaves your perimeter, and you can safely test private APIs that are hidden from the public internet.
4. Operational Integration (The “When”)
Security cannot be a one-off event. The OWASP criteria demands “Operational Fit,” specifically calling for CI/CD integration and automated regression testing to catch vulnerabilities as models evolve.
Noma acts as an automated security gate in your developer pipelines. Beyond just finding bugs, Noma helps you manage the fix. We define specific remediation SLAs, such as mitigating critical findings within 48 hours, and help you prioritize the most critical issues to fix, ensuring your security posture continues to improve.
5. Evaluation Rigor & Transparency (The “Why”)
OWASP encourages only using solutions that provide clear attack chains and reproducible results. OWASP emphasizes the importance of knowing exactly how a vulnerability was exploited.
Noma provides full transparency into every test. Our reports include thread IDs, technique descriptions, and full message traces for every successful attack. We also support “retest after fix” workflows with clear timelines. Ensuring that every mitigation is validated and actually works before you move on.
OWASP Red Flags vs. The Noma Way
The Noma Solution: A Unified AI Security Platform
The OWASP criteria make it clear: effective AI security demands more than point-in-time testing. Noma delivers continuous coverage through three integrated platform pillars that work together in a continuous security improvement cycle.
- AI Security Posture Management (AI-SPM): Continuously discover every AI asset across your environment, from models and agents to data pipelines, MCP servers, and AI-powered tools. Noma maps your entire AI landscape, evaluates risk with deep contextual understanding, and secures your AI supply chain against malicious models, poisoned data, and infrastructure misconfigurations.
- AI Red Teaming: Proactively test your AI applications and agents against the exact attack categories OWASP demands, including prompt injection, tool misuse, excessive agency, and multi-agent coordination failures. Findings flow directly back into AI-SPM to refine risk scores and reprioritize assets.
- AI Runtime Protection: Enforce real-time guardrails on models and agents in production. Noma’s proprietary AI security models analyze prompts, responses, tool calls, and agent behaviors, then detect, mask, or block threats before they impact your business. When runtime detects a novel attack, that intelligence feeds back into posture management and informs future red team scenarios.
Every asset discovered shapes runtime policy. Every red team finding refines your risk posture. Every runtime detection sharpens future testing. One contextual platform, continuous improvement, and the confidence to say yes to AI, safely.
Ready to Secure Your AI?
Stop guessing and start testing with Noma. Contact us to schedule a red-teaming test and demo.